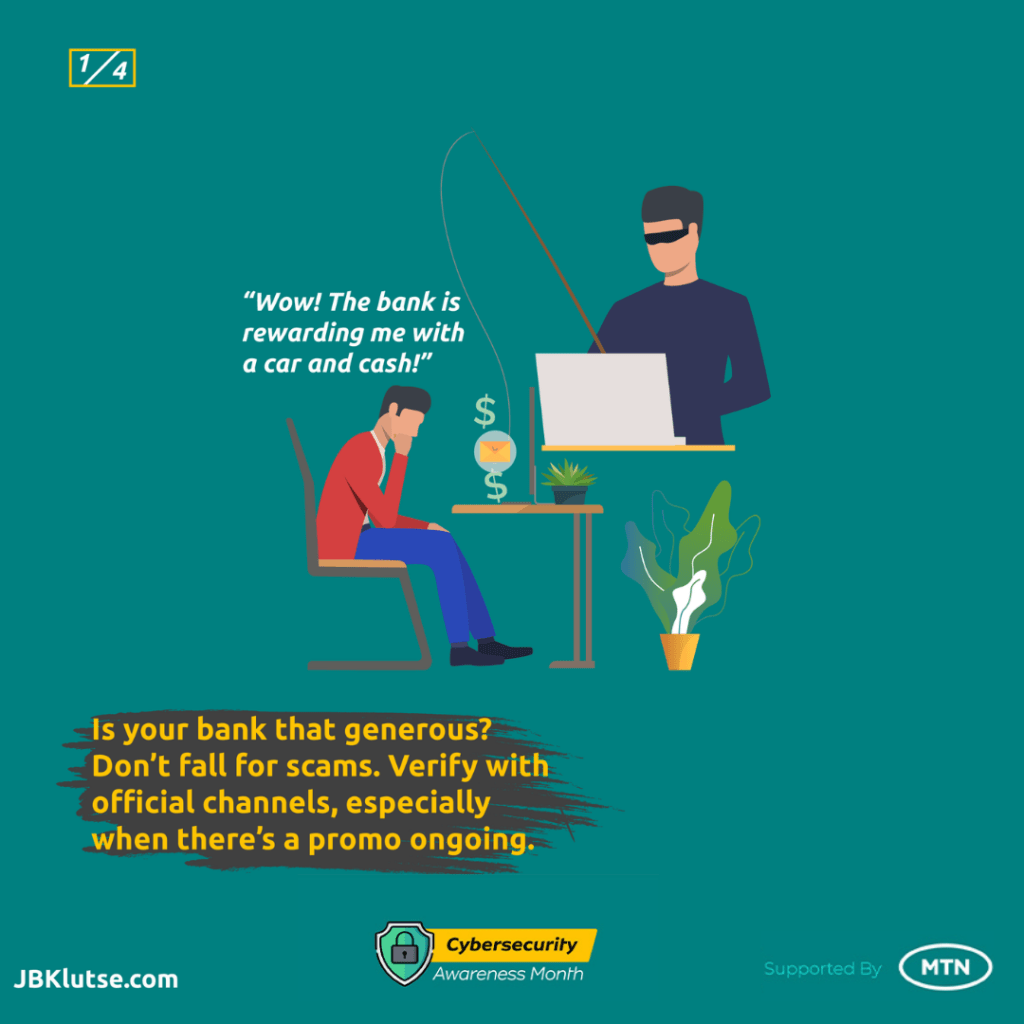
It’s Thursday morning and Mensah sat at his office desk to begin work for the day. As he powered up the computer and started responding to emails received during the night, a subject line caught his attention. He had won a 2019 Honda Accord and all that was required of him was to submit some details to verify his identity.
For the week he’s had dealing with taxi drivers, this is an easy blessing, right? Except that this was no genuine award. It was a phishing attempt – and Mensah was about to fall victim.
Phishing attacks are on the rise, and in a digital-oriented world, more of such should be expected. The criminals have updated their modus operandi with sophistication, however, there are steps you can take to stay ahead of them.
In this article, we’ll learn about phishing and various ways we can keep ourselves from falling victim – no matter what fantastic offers they come up with.
Before we dive in, let’s understand the illustration below.


How attackers present themselves
The legitimate look
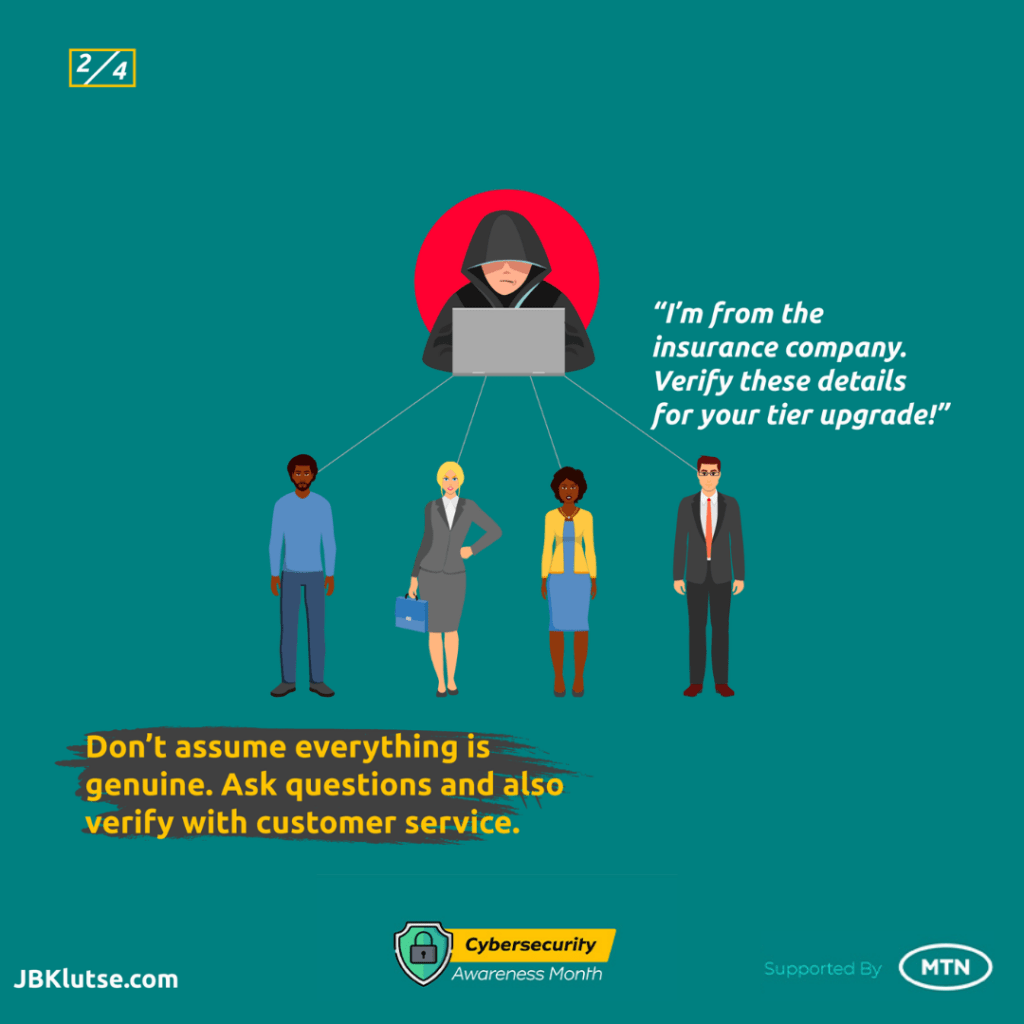
In order for attackers to get you to divulge all the needed information, they’ll have to gain your trust. And to do so, they present themselves either as a work colleague from a different department or a representative of a reputable organization – preferably one that you already have some dealing with.
Your attacker can show up as a field operative of the bank, a labour union you’re affiliated with, or any believable professional profile they can come up with. They’ll come bearing gifts, but as it is with such, their gift becomes a curse.
How phishing is set up
- Through emails
Email attacks are one of the oldest modern-era methods of phishing. Attackers invite their target to leave some personal information in order to redeem a raffle win. They then provide a hyperlink to a Google form or website where you fill out a form and leave them with what they’re after – your important details.
- Through malicious websites
The thing about malicious websites is that they may not necessarily be flagged by Google when you log on to them, and for too many people, that makes the site legitimate. This is because the attackers set their websites up to look as genuine as possible just to keep people from questioning their credentials and motive.
Identifying phishing attacks
While you cannot restrict people from sending you phishing emails, there are some easy common sense measures you can employ to prevent yourself from falling victim to them.
- Observe the grammar and salutation
One of the easiest ways to spot a phishing attempt is by paying attention to their grammar and sentence construction. Most phishing emails are riddled with bad writing and misspelt words. However, while that is true, attackers have also upped their game and can write in a coherent fashion.
- No correspondence? Red flag
Typical phishing attacks are usually a one-off thing, so attackers do not leave room for correspondence – meaning you cannot get back to them and ask questions. Fall for the bait and their work is done.
- Stories don’t add up
If you’re able to have any correspondence with the attacker, you’d notice their stories do not add up. Especially if you know the inner workings of the organization they’re purported to be coming from, you’ll realize they don’t have their facts right and obviously do not qualify to be in the role they claim to be functioning in.
Staying safe from phishing attacks
As noted earlier, most attackers present themselves as representatives of trustworthy organizations and sometimes as work colleagues. Hence the need to go an extra step and verify from the organization the email is supposed to have originated from.
If the email claims to be coming from your bank, reach out to your personal relations officer and be sure their answers are satisfactory enough to allay or confirm your fears.
Here are three (3) to-dos that will keep you safe from falling victim to a phishing attack:
- Do not tap or click on suspicious website links, especially those that look like this (kw1r5a2link) – a mix of alphabets and numbers that don’t make any reading sense.
- Before clicking on an email link, be sure to Google the organization and find out from their social media if they’re running any promotions as stated in the email.
- Trust, but verify. Always follow up with the organization. It will save you 99.99% of the time. If you’re on the right official path, you’ll be asked to carry on. And if you’re about to fall victim to an attack, it’ll be prevented.
To conclude
Cybersecurity and online safety is a personal responsibility. All the public education can be done but if the individual decides to throw caution to the wind, there will be damages.
Again, unless you have a gun held to your head, nothing stops you from making enquiries to verify the genuineness of any claims being made in your email. Don’t be a mugu. Always pick up the phone and make that call to customer service. That’s one of the reasons they exist – to help customers.